- Mixpanel Security Incident: The Mixpanel security incident exposed unauthorized access to internal dashboards affecting Mixpanel AI Mixpanel generative AI and Mixpanel Spark AI features
- AI Analytics Exposure: AI-powered analytics tools operate on large datasets and increase exposure risks if not properly controlled
- Response Measures: Mixpanel responded by tightening access controls updating cookies refining AI permissions and strengthening oversight on integrations and dashboards
- Hidden Risks: Analytics scripts cookies and integrations bypass traditional security layers and require continuous auditing
- SaaS Security Lessons: SaaS teams should apply least privilege principles review AI tools monitor integrations and enforce strict dashboard access controls
The mixpanel security incident captured attention across the SaaS industry because it exposed how deeply analytics platforms sit inside product workflows. Even companies with strong access controls realized that analytics tools often see more user activity than their core applications.
Once the incident surfaced, teams began rechecking scripts, reviewing Mixpanel cookies, inspecting AI-powered analytics features, and confirming how internal dashboards were authorized.
It was not only an isolated flaw. It was confirmation of a broader reality. Modern analytics tools gather granular user actions and connect to multiple internal systems, making them part of the core security boundary rather than optional enhancement modules. The mixpanel security incident proved that clearly.
How The Mixpanel Security Incident Unfolded?
The mixpanel security incident, reported in November 2025, centered on unauthorized access tied to internal dashboards used during monitoring and QA testing. Investigators found that operational environments connected to Mixpanel integrations accessed data outside intended scopes. Some activity involving Mixpanel Spark AI prompted additional scrutiny because AI-driven queries had wider internal access surfaces compared to traditional analytics.
Although the Mixpanel Privacy Policy (updated February 2025) outlines structured controls such as strict access logging and data isolation, real operational environments often accumulate exceptions over time. During the review, Mixpanel’s Safety and Security Committee documented corrective actions, containment steps, and isolation improvements.
Many SaaS teams recognized a deeper implication. AI-enabled analytics such as Mixpanel AI and Mixpanel generative AI, deployed widely in 2024–2025, require broad visibility across large datasets. Without precise oversight, these systems can expand exposure pathways in ways that traditional dashboards never did.
Why This Incident Matters For SaaS Companies?
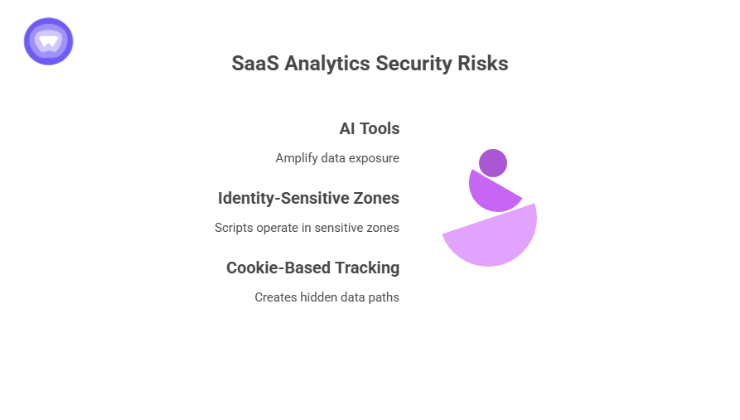
Analytics tools sit directly inside authentication flows, billing sequences, onboarding screens, and user dashboards. This means a compromise does not affect only behavioral data. It intersects with every touchpoint that analytics observes. The mixpanel security incident emphasized three industry-wide shifts.
AI Tools Amplify Data Exposure
Platforms using AI-driven analytics depend on larger volumes of attributes to generate responses. AI-powered dashboards analyze between 10 and 30 times more data fields than legacy BI tools. Source:
This greater reach increases the potential impact of any access lapse.
Analytics Scripts Operate In Identity-Sensitive Zones
A product security review in 2023 reported that 62 percent of SaaS applications embed analytics scripts inside onboarding or login processes.
If analytics components have broad permissions during authentication, an incident gains much deeper reach.
Cookie-Based Tracking Creates Hidden Data Paths
Mixpanel cookies track session continuity, funnels, device identifiers, and metadata used for attribution. Once the incident came to light, companies reassessed how much behavioral data these identifiers carry.
All three factors created a new understanding across the SaaS industry: analytics tools are no longer peripheral. They are central to the security posture.
Hidden Risks Inside Mixpanel Integrations
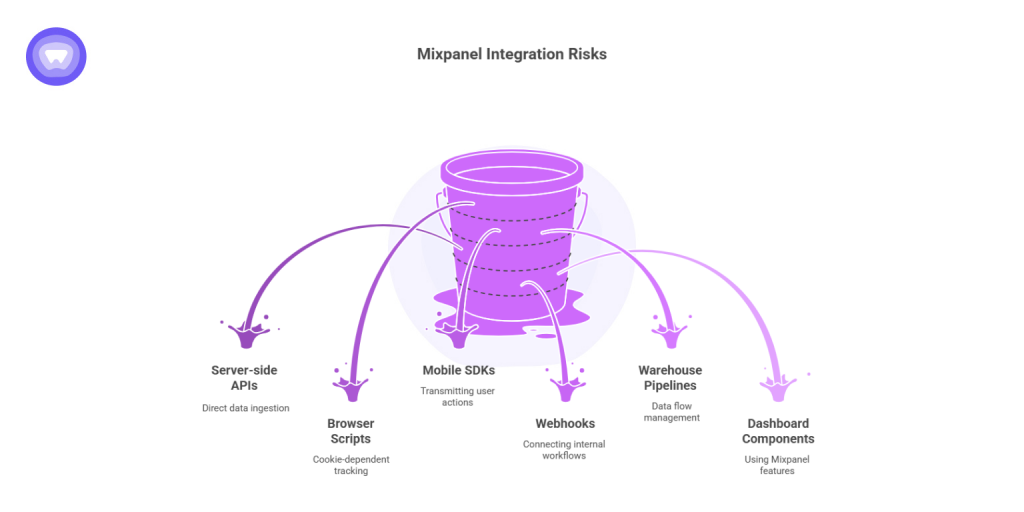
SaaS companies rely heavily on Mixpanel integrations with data warehouses, CRMs, marketing systems, backend APIs, and third party dashboards. Each connector expands the operational footprint.
Key integration channels that increased attention after the mixpanel security incident include:
- Server-side ingestion APIs
- Browser scripts relying on Mixpanel cookies
- Mobile SDKs transmitting user actions
- Webhooks connecting to internal workflows
- Warehouse pipelines
- Dashboard components using Mixpanel features
Teams realized that integrations often bypass standard IAM layers, creating silent data pathways. The incident demonstrated that analytics integrations must receive the same risk assessments as authentication or payment integrations.
How Mixpanel Responded?
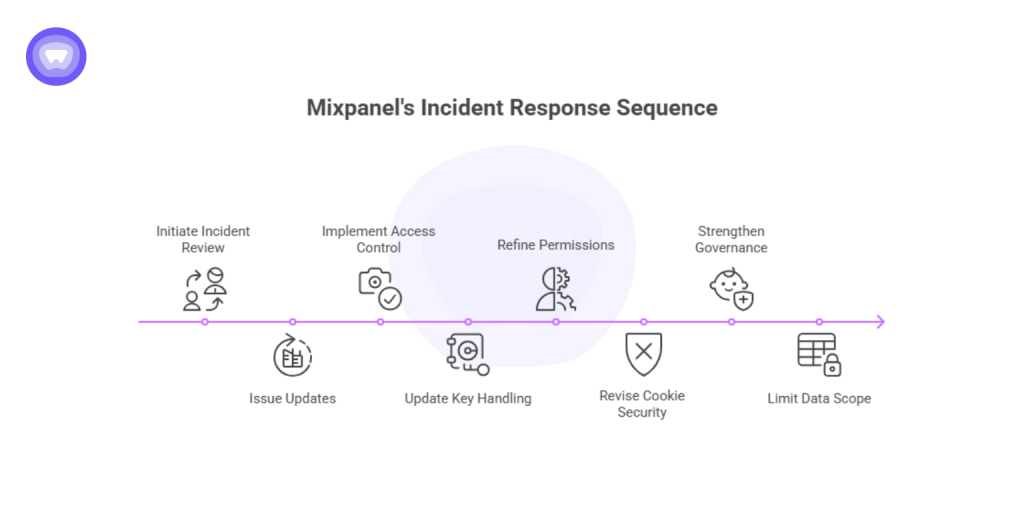
Mixpanel initiated a structured incident review through its Safety and Security Committee. The committee issued updates focusing on transparency and rapid corrective action. Improvements included:
- Tighter access control rules for internal systems
- Secret rotation and key handling updates
- Permissions refinement for Mixpanel AI systems
- Revised cookie security flags
- Strengthened governance aligned with the Mixpanel Privacy Policy
- Stricter data scope limitations for employee dashboards
These adjustments aligned with industry findings. A 2025 security analysis reported a 37 percent reduction in repeat incidents among companies with dedicated AI oversight committees.
Mixpanel’s post-incident steps show a shift toward more granular governance, particularly around AI analytics.
Lessons For SaaS Security Teams

The mixpanel security incident exposed the need for a modern approach to analytics governance. Key lessons include:
Analytics Platforms Hold High Privilege
They process user identity data, behavior history, device details, and session attributes. Any compromise touches sensitive layers.
AI Systems Must Be Reviewed Carefully
Mixpanel AI and Mixpanel generative AI rely on large datasets. Without strict permission boundaries, the scope of access expands automatically as AI features evolve.
Cookie and Identifier Behavior Requires Continuous Auditing
Session continuity and device-level identifiers create exposure points that cannot be treated as low risk.
Dashboards Should Only Access Narrowly Scoped Data
Internal dashboards involved in the incident accessed broader ranges than intended. Least privilege rules must apply to analytics panels as well.
Integrations Expand Attack Surface
Mixpanel integrations bring convenience but introduce additional pathways that must be monitored and controlled.
Key Risks Exposed By The Mixpanel Security Incident
The following table summarizes the primary risks exposed by the mixpanel security incident, highlighting the areas affected, what occurred, and why each risk matters for SaaS security.
| Impact Area | What Occurred | Why It Matters |
| AI Analytics Tools | Mixpanel Spark AI and Mixpanel AI had visibility into broader datasets | AI systems require significant data access and widen exposure |
| Mixpanel Cookies | Session identifiers and funnel attributes were active during compromised operations | Cookies link behavior data to individual users |
| Mixpanel Integrations | Warehouse, CRM, and backend connectors expanded access points | Integrations bypass traditional IAM boundaries |
| Internal Dashboards | QA dashboards accessed unintended data ranges | Shadow environments create risks that escape routine audits |
| Governance Controls | Adjusted by the Safety and Security Committee | Reinforced the importance of continuous oversight |
How The Incident Reshapes SaaS Security Standards?
The mixpanel security incident has become a reference point for reassessing how SaaS companies classify critical systems. Historically, analytics was viewed as non-critical. Yet analytics now sits at the intersection of product navigation patterns, lifecycle events, identity management, and AI-driven personalization.
A SaaS Security Report observed that 48 percent of recent incidents involved systems not originally labeled as critical.
This finding aligns with what the incident revealed. Any system observing user actions or session identifiers requires the same level of scrutiny as authentication, access management, or data storage tools.
Future security expectations for analytics platforms will include:
- AI permission segmentation
- Dashboard-level zero trust policies
- Cookie and identifier minimization frameworks
- Integration verification workflows
- Event-level encryption standards
Companies are now expected to maintain these controls internally, not rely entirely on vendor assurances.
Where PureWL White Label VPN Solution Supports These Security Shifts
Once the mixpanel security incident prompted teams to isolate access points, organizations began moving analytics dashboards, monitoring panels, and internal consoles into protected network zones. PureWL White Label VPN Solution supports this shift by helping companies restrict access to internal analytics environments.
With controlled network ranges, encrypted tunnels, and IP-specific rules, companies create secure boundaries for AI tools, QA dashboards, and operational consoles. This reduces the risk of cross-environment access and limits exposure during audits or post-incident reviews.
SaaS teams using analytics systems with wide integration layers rely on PureWL White Label VPN Solution to define who can reach sensitive interfaces, ensuring that privileged tools remain protected even during high-risk periods.
A Stronger Foundation After The Mixpanel Security Incident
The mixpanel security incident reshaped how SaaS teams perceive analytics security. It highlighted the need for strict access rules, continuous oversight, AI-specific controls, and secure network boundaries. Companies that reevaluate their analytics infrastructure now will establish stronger trust with customers and create a more resilient security posture.
By treating analytics platforms as high-access systems instead of peripheral add-ons, organizations build an environment where visibility, privacy, and operational safety can coexist with performance and innovation.


