- Vect ransomware is a modern double-extortion threat: It encrypts systems and steals data to increase pressure on victims.
- Primary attack methods include stolen credentials and phishing: Weak or exposed remote access systems are commonly exploited entry points.
- Ransomware operations follow structured attack stages: Intrusion, lateral movement, data theft, and delayed encryption are used to maximize damage.
- Remote work and weak access controls increase risk exposure: Poor identity management and unsegmented networks remain key vulnerabilities.
- Strong access security reduces ransomware impact: Identity protection, secure remote access, and segmentation help limit attack success.
Most ransomware groups announce themselves loudly. They leak stolen files, flood media headlines, and leave behind visible chaos. Vect operates differently.
Security researchers tracking recent attacks describe Vect ransomware as controlled, selective, and heavily focused on operational disruption. Instead of relying on noisy mass campaigns, attackers behind Vect appear to target weak access points, move quietly through networks, and lock systems only after valuable data has already been identified.
That shift reflects a larger change happening across the ransomware ecosystem. Modern attacks are no longer random spam operations targeting anyone with an email address. They are organized intrusion campaigns designed to exploit remote access systems, unmanaged endpoints, exposed credentials, and weak network segmentation.
Vect ransomware has become another example of how cybercriminal groups are refining their methods while businesses continue relying on outdated security assumptions.
What Is Vect Ransomware?
Vect ransomware is a malware strain associated with data encryption, extortion, and operational disruption. Once inside a network, the malware encrypts files and systems, making them inaccessible until a ransom payment is made.
Like many modern ransomware operations, Vect appears to follow a double extortion model:
| Attack Stage | What Happens |
| Initial Access | Attackers gain entry through stolen credentials, phishing, or exposed systems |
| Network Movement | Internal systems and sensitive data are mapped |
| Data Exfiltration | Important files are copied before encryption begins |
| Encryption Deployment | Files and systems become inaccessible |
| Extortion Phase | Victims face pressure to pay for recovery and data suppression |
This model increases pressure on victims because restoring encrypted systems alone no longer resolves the incident. Sensitive data may already be in criminal hands before the ransom demand appears.
Ransomware attacks continue to evolve toward multi-stage operations involving credential theft, lateral movement, and data theft rather than simple file encryption.
Why Ransomware Groups Are Changing Their Tactics
The ransomware landscape of 2026 looks very different from the attack environment businesses faced just a few years ago.
Older ransomware campaigns focused on volume. Attackers sent large phishing waves and hoped a percentage of targets would click malicious links. Today, attackers often behave more like organized intrusion teams.
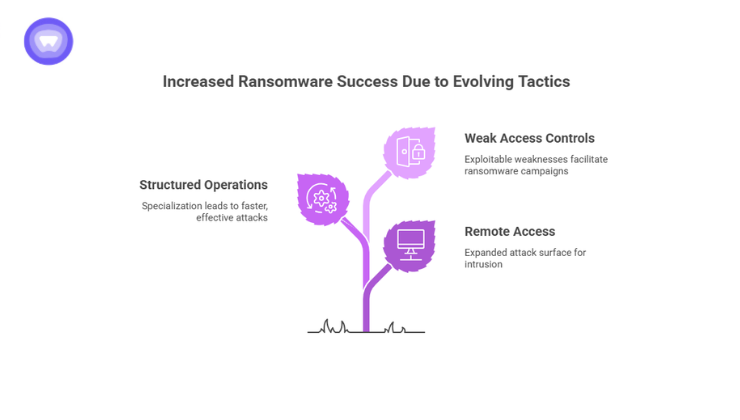
Several developments accelerated this shift:
Remote Access Became a Permanent Attack Surface
Hybrid work environments expanded the number of exposed endpoints connected to corporate systems. Remote desktop services, unmanaged devices, cloud platforms, and third-party access points created more opportunities for intrusion.
The IBM Cost of a Data Breach Report found that compromised credentials remained one of the most common attack vectors in recent enterprise breaches, with remote environments increasing exposure risks.
Cybercriminal Operations Became More Structured
Modern ransomware groups increasingly operate like businesses. Some specialize in malware development while others handle negotiations, infrastructure management, or initial network access.
This specialization created faster and more effective attacks.
Businesses Still Depend on Weak Access Controls
Many organizations still expose sensitive systems through:
- Shared credentials
- Poor VPN management
- Open remote desktop ports
- Unsegmented networks
- Unsecured third-party access
Vect ransomware campaigns appear to exploit exactly these weaknesses.
How Vect Ransomware Infiltrates Networks
Ransomware attacks rarely begin with encryption. The real damage starts much earlier.
Attackers generally spend time inside networks before deploying ransomware payloads. During this phase, they identify high-value systems, security gaps, and backup infrastructure.
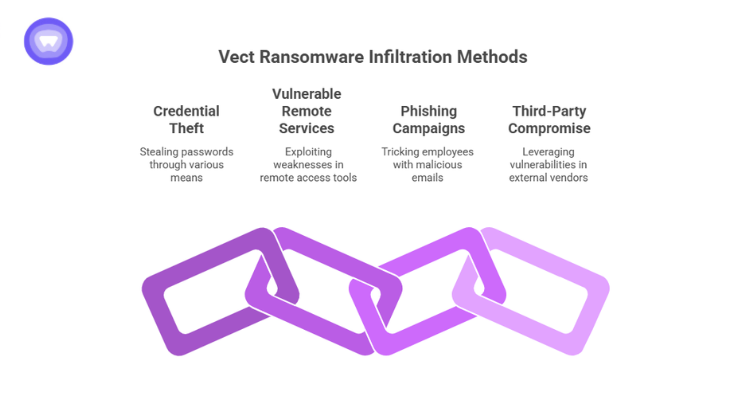
Common intrusion methods linked to ransomware operations include:
Credential Theft
Stolen passwords remain one of the easiest ways into corporate environments.
Attackers obtain credentials through:
- Phishing pages
- Malware infections
- Password reuse
- Data breach leaks
- Session hijacking
A report noted that credential abuse continues to play a major role in security incidents worldwide.
Vulnerable Remote Services
Remote access tools are frequent ransomware entry points.
Attackers actively scan for:
- Exposed RDP services
- Weak VPN authentication
- Unpatched remote access software
- Misconfigured cloud gateways
Once access is established, attackers often escalate privileges and move laterally across systems.
Phishing Campaigns
Email-based attacks remain highly effective because they target employees directly.
A single malicious attachment or credential harvesting page can give attackers an initial foothold inside an organization.
Third-Party Compromise
Vendors, contractors, and external service providers can unintentionally expose business networks when access controls are weak.
This risk becomes more severe when organizations lack segmented access permissions.
The Business Impact of Vect Ransomware

Ransomware damage extends far beyond encrypted files.
Businesses impacted by ransomware often face:
- Operational downtime
- Customer trust erosion
- Financial losses
- Regulatory investigations
- Data exposure risks
- Long recovery timelines
The average financial impact of ransomware incidents has continued rising as attacks increasingly target operational infrastructure rather than isolated devices.
Recovery costs for ransomware victims remained substantial across industries due to downtime, remediation, and operational disruption.
For smaller organizations, even a short disruption can interrupt revenue, supply chains, and customer services.
Why Traditional Security Layers Often Fail
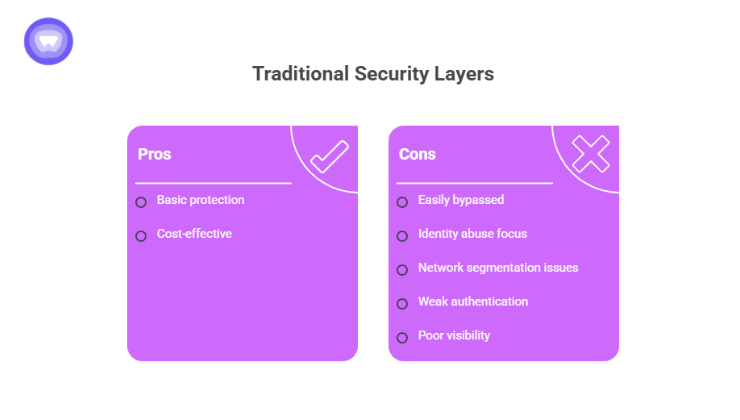
Many organizations still assume antivirus software alone can stop ransomware. Modern attacks bypass that assumption quickly.
Vect ransomware reflects a broader reality: attackers now focus heavily on identity abuse and network access weaknesses rather than obvious malware delivery alone.
Several gaps commonly contribute to successful ransomware attacks.
Flat Network Structures
When systems are poorly segmented, attackers can move across departments and servers after initial access.
Weak Authentication Policies
Single-factor authentication remains a major liability for remote access systems.
Poor Visibility Into Remote Activity
Organizations often lack centralized visibility into:
- Remote login behavior
- Unauthorized geographic access
- Suspicious account activity
- Credential sharing
Inconsistent Access Control
Third-party users and distributed teams frequently receive broader access permissions than necessary.
These weaknesses create ideal conditions for ransomware operators.
Signs a Ransomware Intrusion May Already Be Underway
Ransomware deployment is usually the final stage of a larger intrusion operation.
Businesses often miss earlier warning signs such as:
| Early Indicator | Potential Meaning |
| Multiple failed login attempts | Credential stuffing or brute force activity |
| Unusual VPN logins | Unauthorized remote access |
| Privilege escalation activity | Attackers expanding control |
| Disabled security tools | Attempted defense evasion |
| Large outbound data transfers | Possible data exfiltration |
| Unexpected administrator accounts | Persistence mechanisms |
Detecting these indicators early can significantly reduce damage.
Why Secure Remote Access Matters More Than Ever
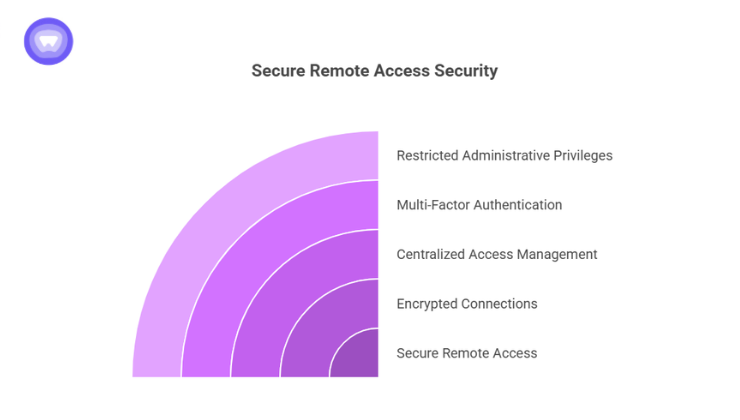
Modern ransomware attacks frequently begin through remote access weaknesses.
Businesses operating with distributed teams, contractors, and cloud-based workflows require secure access systems that reduce exposure without complicating operations.
Strong remote access security includes:
- Encrypted connections
- Centralized access management
- Multi-factor authentication
- Restricted administrative privileges
- Segmented network access
- Activity monitoring
Without these controls, remote access infrastructure becomes a direct pathway into internal systems.
The Growing Role of White Label VPN Infrastructure
As cyber threats expand, many businesses are integrating secure connectivity directly into their platforms and services instead of relying on fragmented third-party tools.
White label VPN infrastructure allows organizations to deploy branded secure access environments while maintaining centralized control over authentication, encryption, and user management.
This approach becomes especially relevant for:
- SaaS providers
- Managed service providers
- Enterprise platforms
- Fintech ecosystems
- Remote workforce platforms
Businesses increasingly want secure connectivity built into the user experience rather than treated as a separate security layer.
How PureWL Supports Secure Access Environments
PureWL by PureVPN provides white label VPN infrastructure that helps businesses deploy secure remote access under their own brand identity without building VPN architecture internally.
For organizations concerned about ransomware exposure, centralized VPN management and encrypted connectivity can reduce risks tied to unsecured remote access, credential interception, and unmanaged network traffic. Features such as scalable deployment, Dedicated IP support, and controlled user access align with the growing demand for secure distributed environments.
Rather than treating cybersecurity as an isolated add-on, businesses are increasingly embedding secure connectivity into their platforms and operational workflows. That shift reflects how ransomware threats like Vect continue targeting weak access pathways first.
Final Thoughts
Vect ransomware is not important because it is unique. It matters because it reflects where cybercrime continues to move.
Attackers are becoming quieter, more organized, and more focused on access control failures rather than noisy malware tactics alone. Businesses still relying on fragmented remote access systems, weak credential policies, and unmanaged connectivity face increasing exposure as ransomware operations evolve.
The organizations recovering fastest from ransomware incidents are not simply buying more security tools. They are reducing attack surfaces, tightening access controls, segmenting infrastructure, and treating remote connectivity as a critical security layer rather than a convenience feature.
Ransomware groups adapt quickly. Defensive strategies must evolve faster.


