As of February 2026, Conduent confirmed that at least 25 million individuals were affected by an ongoing data breach tied to systems processing US government services. Notifications are still rolling out, and the number is expected to rise as forensic reviews continue across multiple states.
The breach is among the largest involving public benefits infrastructure in recent years and underscores systemic risk in government outsourcing.
- The Conduent data breach affected over 25 million individuals, exposing sensitive personal, financial, and medical information.
- Government contractors managing citizen data face high concentration risk, making them prime targets for cyberattacks.
- Inconsistent security mandates, fragmented oversight, and uneven incident reporting amplify vulnerabilities in the government outsourcing model.
- Secure remote access, segmented infrastructure, centralized authentication, and monitoring are critical risk controls for contractors handling regulated data.
- Solutions like PureWL White Label VPN provide state-specific segmented tunnels, dedicated IPs, and controlled access, reducing exposure and supporting compliance with vendor audits.
What Conduent Does and Why It Matters?

Conduent is a Fortune 500 business process services provider that spun out of Xerox in 2017. It manages high-volume public sector operations, including:
- Medicaid claims processing
- Unemployment insurance systems
- Child support platforms
- Electronic toll collection
- Traffic and parking citation systems
The company handles transactions for hundreds of millions globally. In the US, it operates as a backend processor for multiple state agencies.
The concentration of citizen data across programs and states means one compromise affects entire administrative ecosystems, not just a single database.
Confirmed Scope: 25 Million and Climbing
Breach notifications and state disclosures confirm at least 25 million individuals were affected. Compromised data includes:
- Names
- Social Security numbers
- Dates of birth
- Physical addresses
- Medicaid identification numbers
- Financial account details in some programs
- Limited medical information in certain jurisdictions
The notifications are rolling out over weeks, indicating the breach spans multiple segmented systems and the full scope is still being determined. This pattern is consistent with large-scale contractor breaches involving multi-tenant infrastructure.
Timeline Gaps and Disclosure Concerns
Several critical details remain unclear:
- The exact date of initial intrusion has not been disclosed
- The duration of attacker access is unreported
- Technical methods used remain unconfirmed
Prolonged dwell time is common in contractor breaches. A report notes that 62 percent of third-party or supply chain breaches took weeks or months to detect fully. This lag highlights the complexity of mapping multi-state, multi-program systems.
How the Attack Happened
While Conduent has not publicly confirmed technical specifics, the breach aligns with patterns observed in recent ransomware and data theft campaigns targeting government contractors.
- Credential Compromise: Nearly half of breaches involve stolen credentials, allowing lateral movement in multi-tenant environments.
- Vulnerability Exploitation: Unpatched APIs, portals, and remote access appliances remain high-risk points.
- Data Exfiltration Before Encryption: Large-scale incidents often exfiltrate sensitive data prior to any encryption or disruption.
IBM’s 2024 report indicates that 80 percent of ransomware-related breaches included data theft. This pattern is consistent with Conduent’s breach, which appears to prioritize exfiltration over disruption.
Why Government Contractors Are High-Value Targets
Government outsourcing centralizes sensitive citizen data inside private infrastructure. Contractors often hold:
- Social Security numbers
- Benefit records
- Payment histories
This concentration makes them high-value targets. One compromise can impact multiple states simultaneously.
- Average US breach cost: $9.48 million
- Identity theft reports in 2023: 1 million+
- Ransomware breaches involving data theft: 80%
The Conduent breach combines high data sensitivity, multi-state exposure, regulatory scrutiny, and long-term identity theft risk, elevating it beyond a routine corporate incident.
Impact on States and Citizens
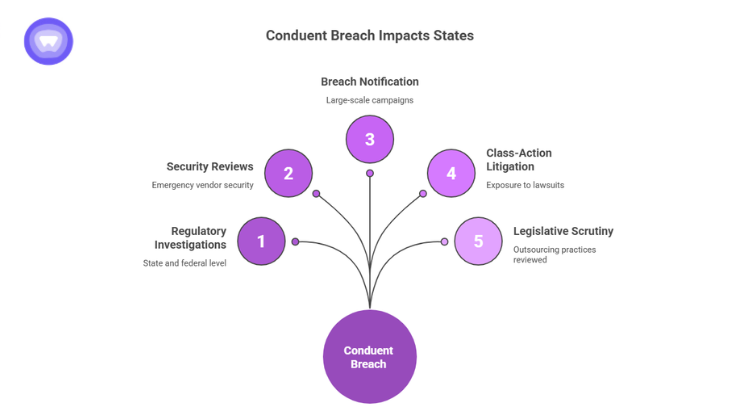
When a contractor like Conduent reports 25 million affected individuals, the operational shock lands first on state agencies. States now face:
- Regulatory investigations at the state and federal level
- Emergency vendor security reviews
- Large-scale breach notification campaigns
- Exposure to class-action litigation
- Legislative scrutiny over outsourcing practices
For agencies that outsourced processing to reduce operational overhead, the breach converts cost savings into reputational and legal risk. For individuals, the impact is more personal and more enduring.
The Federal Trade Commission recorded more than 1 million identity theft reports in 2023. Government benefits fraud remains a persistent category within those complaints. When Social Security numbers, Medicaid IDs, and dates of birth are exposed together, identity misuse does not peak in the first 30 days. It can surface years later.
Unlike passwords, these identifiers cannot be reset. That permanence changes the risk profile entirely.
This is not just a breach story. It is a signal event for any organization that processes regulated data on behalf of public agencies.
Structural Weakness Exposed
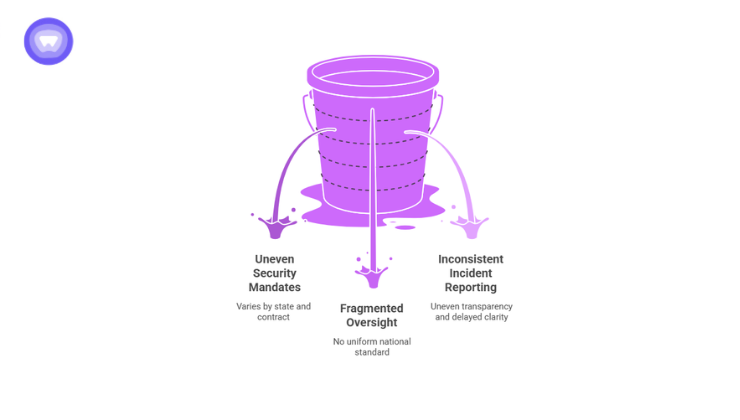
Large contractor breaches expose systemic design flaws, not isolated mistakes. The Conduent incident highlights three structural gaps in the government outsourcing model:
1. Uneven Security Mandates
Federal agencies operate under defined cybersecurity frameworks. Contractors, however, are bound only by what procurement contracts specify. Security requirements vary by state and by contract language.
2. Fragmented Oversight
Each state maintains its own oversight process. There is no uniform national standard governing third-party infrastructure handling citizen data across all programs.
3. Inconsistent Incident Reporting
Breach notification timelines and disclosure obligations differ across jurisdictions. This creates uneven transparency and delayed public clarity.
When a single vendor supports Medicaid, unemployment, and other services across multiple states, concentration risk increases sharply. A compromise inside one infrastructure stack becomes a multi-state exposure event.
For technology providers and managed service operators, this reinforces a clear reality. Multi-tenant environments handling regulated data demand strict segmentation and tightly governed remote access.
Key Metrics in Context
These figures are not abstract. They illustrate the financial, operational, and societal weight of a single contractor compromise.
| Category | Data |
| Confirmed affected individuals | 25 million+ |
| Data types exposed | SSNs, DOB, addresses, Medicaid IDs, financial and medical data |
| Average US breach cost | $9.48M |
| Ransomware breaches involving data theft | 80% |
| Identity theft reports in 2023 | 1M+ |
For service providers building platforms that support public agencies, exposure at this scale is an existential risk.
Infrastructure Lessons for Service Providers
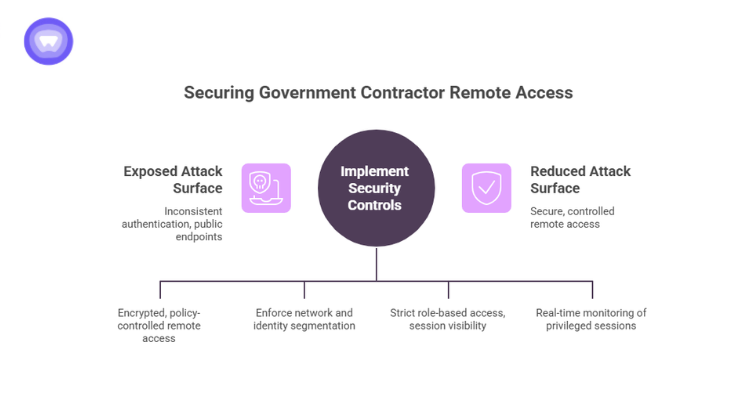
The Conduent breach is a case study in architectural exposure. Large-scale contractor incidents typically reveal weaknesses in four core areas:
- Remote Administrative Access
Government contractors operate distributed teams, third-party integrators, and support personnel across regions. If administrative access relies on exposed public endpoints or inconsistent authentication enforcement, the attack surface expands rapidly.
Encrypted, policy-controlled remote connectivity should be the baseline. Not an afterthought.
- Multi-Tenant Segmentation
When multiple state programs run on shared backend infrastructure, segmentation must be enforced at both network and identity layers. Logical separation alone is insufficient.
Segregated environments prevent lateral movement if one tenant environment is compromised.
- Credential Governance
In contractor environments, privileged accounts require strict role-based access and session visibility. Without centralized control, credential sprawl becomes a liability.
- Continuous Monitoring
Extended dwell time increases the volume of exfiltrated data. Real-time monitoring of privileged sessions and network behavior reduces containment delays. For service providers in the government ecosystem, these controls are not optional enhancements. They are operational safeguards.
Where PureWL White Label VPN Fits
Remote access remains a primary attack vector for contractors. Administrative dashboards, vendor portals, and backend APIs are frequently exposed, increasing risk across multi-state systems. A controlled architecture with encrypted tunnels, centralized authentication, and client-level segmentation limits lateral movement, credential abuse, and cross-client exposure. Isolating each client environment prevents one compromise from cascading across multiple states.
PureWL White Label VPN Solution enables service providers and government contractors to deploy branded VPN infrastructure with dedicated IPs, segmented state-specific tunnels, and centralized access control. Administrative sessions are fully authenticated and logged, providing measurable security aligned with vendor audits.
For organizations handling regulated public data, structured remote connectivity functions as a critical risk control rather than an optional feature.
Final Thoughts
The Conduent breach is not simply a 25 million record incident. It is a structural warning to every organization handling citizen data at scale. When governments centralize sensitive information inside private contractors, the contractor’s security posture becomes a matter of public trust.
Segmented environments, encrypted administrative access, centralized authentication, and continuous monitoring are now baseline requirements. Service providers that embed these controls will be better positioned to meet rising oversight and protect critical public sector data.


