The Oracle data breach 2025 is no small story. A critical vulnerability—CVE-2021-35587—was exploited in Oracle’s systems, and the fallout has been massive. This isn’t just about one company. It’s about the real risks hiding in enterprise infrastructure. The type of risks that affect you, your clients, and your partners—even if you’re not an Oracle customer directly.
Let’s walk through what happened, why it matters, and what you should be doing now to keep your business safe.
What Really Happened in the Oracle Data Breach?
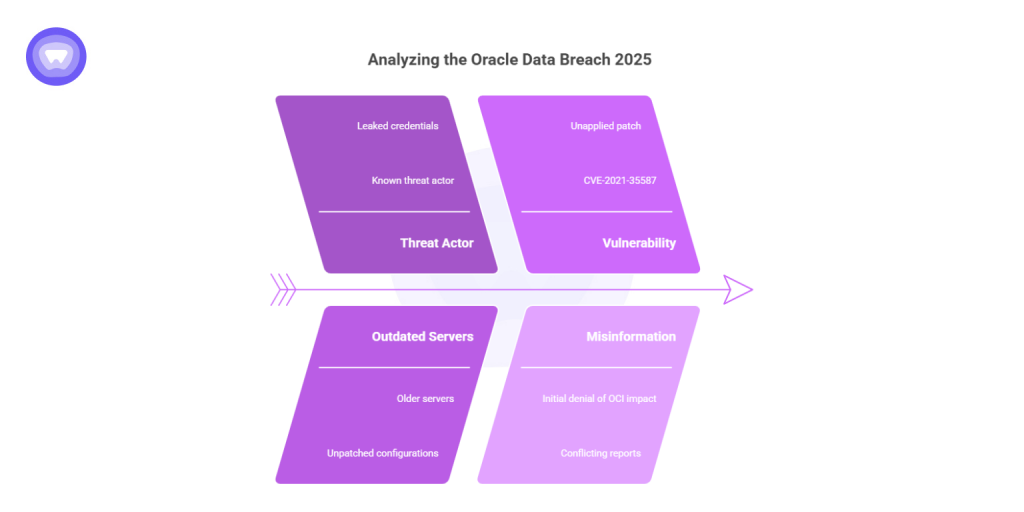
The Oracle data breach 2025 came to light after a known threat actor, operating under the alias “rose87168,” leaked database access credentials linked to several Oracle services. The data reportedly came from older Oracle servers running outdated configurations—some of which hadn’t been patched in years.
The point of entry? A previously disclosed vulnerability: CVE-2021-35587. It’s a privilege escalation bug found in Oracle WebLogic Server. While Oracle issued a patch years ago, many businesses hadn’t applied it. That mistake opened the door for attackers.
Oracle initially stated that Oracle Cloud Infrastructure (OCI) wasn’t impacted. But soon after, multiple reports challenged that claim. While it’s still unclear exactly which services were exposed, leaked credentials point toward widespread access across development and staging environments. The Oracle cloud data breach was much larger than early statements suggested.
Which Oracle Systems Were Targeted?
| Service Type | Risk Level |
|---|---|
| Legacy WebLogic Servers Mitigation: Immediately patch CVE‑2021‑35587, apply strict firewall rules, and isolate vulnerable instances from production networks. | High |
| Hybrid Cloud Components Mitigation: Audit hybrid connections, review access controls, and harden configurations to reduce misconfiguration risks. | Medium |
| OCI Production Environments Mitigation: Maintain standard patching, enable continuous monitoring, and follow Oracle’s security advisories. | Low |
Attackers weren’t interested in customer-facing dashboards. They were after backend access—config files, credentials, infrastructure metadata, and logs. These are the keys to the kingdom in cloud environments.
According to leaked documents and security bulletins:
- Legacy Oracle WebLogic servers were vulnerable.
- Some Oracle Cloud regions still ran hybrid components using legacy code.
- Internal admin interfaces were exposed through misconfigured ports.
- Oracle America Inc data breach reports noted compromised developer SSH keys.
The Oracle America data breach confirms that even high-level internal users had their accounts accessed. This wasn’t just a minor incident—it was a systemic failure in security hygiene.
What Data Was Stolen?
2. Remove old public keys from servers.
3. Generate new key pairs using
ssh-keygen.4. Update your CI/CD pipelines and services with the new keys.
5. Distribute securely and enforce rotation policies.
2. Generate new tokens with limited scopes.
3. Update application secrets or environment variables.
4. Enable refresh tokens with expiry policies.
5. Monitor token usage via audit logs.
2. Store backups in isolated, access-controlled vaults.
3. Rotate storage credentials periodically.
4. Validate integrity with checksums or digital signatures.
5. Implement disaster recovery drills to ensure readiness.
While the full Oracle data breach list is not public, here’s what’s known:
- Usernames and hashed passwords
- SSH keys and access tokens
- Environment variables (including database strings)
- Configuration backups
- OAuth tokens for third-party services
This breach isn’t about raw customer data—it’s about access. The stolen assets allow attackers to move laterally inside corporate networks or impersonate admin accounts in cloud systems. That’s far worse than a one-time data dump.
Who Was Affected?
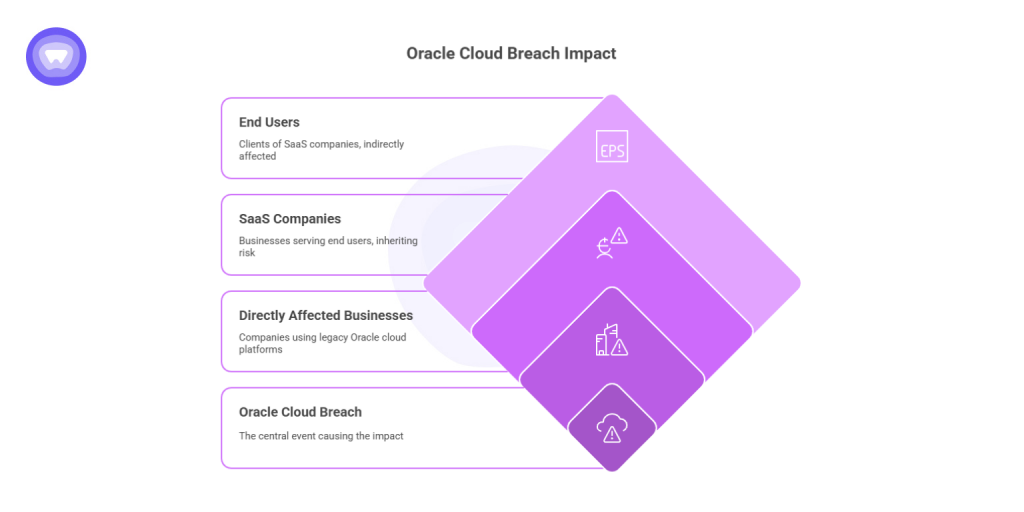
The exact number of businesses impacted by the Oracle cloud breach company list hasn’t been published yet. However, internal leaks suggest that thousands of small and mid-sized businesses relying on legacy Oracle cloud platforms might be affected.
How many people were affected by the Oracle data breach? That depends on the reach of each impacted customer. SaaS companies serving thousands of end users, for instance, might have unknowingly exposed client data through inherited risk.
Legal Fallout: Lawsuits and Settlements
With major cloud vendors like Oracle, legal action is inevitable when things go south.
The Oracle data breach lawsuit has already kicked off, with class action filings emerging in multiple states. Plaintiffs claim Oracle failed to follow its own patching policies and did not disclose the breach in a timely manner.
This has led to talks of a large Oracle breach settlement, though the total figure is still speculative.
Victims are also asking: What is the Oracle data breach settlement payout date? As of now, no date is confirmed. Based on past cases, it could be 12–18 months before checks go out—if at all.
The Bigger Picture: Supply Chain Risk and Shadow IT
This breach highlights a growing issue in tech: supply chain risk.
Even if your systems are patched and secure, the tools you rely on may not be. Many companies don’t even know which services are powered by Oracle in the background. That’s the problem with shadow IT—infrastructure that runs without your direct control.
A vulnerability in your CRM vendor could compromise your customer data. An old API integration could leak your credentials. It’s all connected.
What You Can Do Now?
Here’s a short action plan:
- Audit your stack – Check if any vendor uses Oracle infrastructure.
- Reset credentials – Especially for admin users or integrations.
- Patch aggressively – Don’t wait for news headlines to act.
- Monitor unusual traffic – Especially to OCI or cloud endpoints.
- Encrypt internal traffic – Add another layer between users and your backend.
This is where tools like a VPN come into play.
Why Businesses Need VPNs in a Post-Breach World?
The biggest lesson? You can’t rely on vendors to protect you.
Running traffic through a secure, encrypted tunnel can prevent third-party breaches from leaking your data. A business VPN masks IPs, hides login attempts, and restricts access to critical assets—even if your endpoint is compromised.
A white label VPN lets you offer this security to your customers. It builds trust, improves compliance, and keeps data private in transit.
Want to Offer That Kind of Protection? Don’t Build—Resell
Setting up your own VPN from scratch takes months. It’s expensive, messy, and hard to maintain. But with a white-label partner, you can go to market fast.
PureWL: Help Your Clients Stay Ahead of Breaches Like Oracle’s
If you serve agencies, startups, SaaS tools, or eCommerce brands—they all need protection. With PureWL, you can launch your own VPN in days:
- Branded apps across platforms
- No coding or server setup
- Full access control via an easy VPN panel
- Support for compliance, GDPR, and zero-logging
- Industry-grade encryption using OpenVPN and WireGuard
- Auto updates, kill switch, DNS leak prevention
No infrastructure. No legal hurdles. Just a clean, fast way to help your clients stay safe—and profit while doing it.


